Manage members and groups
Manage members and groups
This is for:
System AdministratorThe members of your Coveo organization are organized by groups to ease privilege management. The members of a group are granted a set of privileges, which determines which features and data of Coveo these group members can access.
Coveo organizations come with built-in groups, which you can use, duplicate, or edit. You can also create your own groups.
The following is an overview of these original tasks but, as mentioned previously, you can edit the privilege set of a group at any moment. You can also refer to the comparison tables to review the privileges granted by default to each built-in group.
Built-in groups
A Coveo organization comes with several built-in member groups. Each group is granted a set of privileges that gives the members access to the tools required to accomplish their tasks in the Coveo Administration Console.
The Coveo built-in groups have already been granted a set of privileges that’s appropriate for their duties. You can edit these groups and add members to them.
|
|
Leading practice
Before adding members to a built-in group, you should revise the default privilege set of that group to ensure that it’s in accordance with your business' hierarchy of responsibilities. |
Alternatively, you can create a new group from scratch, and optionally grant it a privilege set via the Template menu.
The Coveo built-in groups have been created with specific duties in mind. The following is an overview of these original tasks but, as mentioned previously, you can edit a group’s privileges at any moment.
Administrators
Members of the Administrators group have the highest access level for all privileges and can create resources in all domains. You should therefore only allow a few select users in the Administrators group of your Coveo organization.
The Administrators group is the only one that can manage search pages. They can modify your organization settings and implement a single sign-on method for organization members to use at login. Furthermore, administrators can access all the indexed content and query logs for troubleshooting purposes. They can also receive notifications about any type of activity occurring in the organization.
Analytics managers
Analytics managers can manage usage analytics, that is, edit dimensions, named filters, reports, etc.
Analytics viewers
Members of the Analytics Viewers group can access the reports that the analytics managers allowed them to see, but can’t edit these reports. The analytics viewers' job typically requires them to review your organization usage analytics and draw conclusions.
Content managers
Content managers have the privileges required to index content and customize how and what’s retrieved. They can edit sources, fields, and indexing pipeline extensions. They can also execute queries in the Content Browser to ensure data is adequately indexed. Moreover, if you have sources that index the permission system of the original repository, content managers can manage and troubleshoot security identities and security identity providers.
Relevance managers
Relevance managers are typically responsible for optimizing the capabilities of your Coveo solution. They can fine-tune query pipeline components such as ranking rules and featured result rules, create Coveo Machine Learning (Coveo ML) models that will learn from user behavior and help return the most relevant content, and create reports to analyze the impact of their changes.
Users
Members of the Users group can access and use your Coveo-powered search interfaces, but can’t make any changes in the Coveo Administration Console.
|
|
Merchandisers group
Merchandisers shape the presentation and visibility of product content within Coveo. Their responsibilities often include influencing the appearance and ranking of search results, managing product recommendations, and optimizing the overall user search experience. Although not yet part of built-in groups, you can still create your own merchandiser specific group and select Merchandisers template in the "Privileges" tab to grant them the privileges they need. |
Add or edit a group
|
|
Note
Coveo Support employees aren’t authorized to grant privileges to customers in a Coveo organization. If you want to be granted access to a Coveo organization, you must follow the access request workflows of your company. |
On the Groups (platform-ca | platform-eu | platform-au) page, click Add group to add a new group. To edit a group, on the Groups (platform-ca | platform-eu | platform-au) page, select the desired group from the list, and then click Edit in the Action bar.
On the Add group/Edit a group subpages, the "Configuration" tab is shown by default. Other tabs are "Members", "Privileges", and "Access."
"Configuration" tab
In the Group name box, enter a name for your group.
|
|
Leading practice
Use role-related names for group names such as |
"Members" tab
|
|
Note
The Members tab isn’t available when creating a group, so skip to the Privileges tab. Once you’ve completed the group creation process, you’ll need to edit your new group to add members to it. |
The Members tab lets you add members to a group. There are two ways to do so:
-
Import a group of members from an OpenID domain, Salesforce user profiles, or single sign-on provider.
-
Add a single member manually.
You can also remove members from the group through the Members tab.
Import members
You can add several members at once to a group by selecting an OpenID domain, single sign-on groups, or Salesforce user profiles. The corresponding users will then be able to log in to your organization.
-
Log in to Coveo (platform-ca | platform-eu | platform-au) with a user from the same OpenID domain as the users you want to add.
ExampleSelect Log in with Salesforce to add members from a Salesforce group.
Similarly, to add users retrieved from a single sign-on (SSO) identity provider, log in using the SSO.
-
On the Groups (platform-ca | platform-eu | platform-au) page, click the group to which you want to add the identity set, and then click Edit in the Action bar.
-
On the Edit a group subpage, in the "Members" tab, under Include the following identities, select an OpenID domain, single sign-on groups, or Salesforce user profiles to add to the group.
Notes-
The SSO provider groups displayed in the Identity set menu are the groups provided in the
user.groupsattribute of the identity provider assertion. Therefore, only SSO provider groups in which your account is included are available; as an administrator, you may therefore want to be a member of all groups. This limitation doesn’t apply when configuring this feature via API calls rather than with the Coveo Administration Console. -
SSO provider groups are available in the dropdown menu only once you have:
-
Completed the SSO configuration procedure.
-
Logged in to Coveo using the SSO option.
-
-
-
Click Save.
NoteAlthough the users in the identity sets you import into your organization can access Coveo, they don’t appear on the organization member list.
Add specific members to a group
You can individually invite people to a group, which is useful when a group should contain only a few users.
-
On the Members tab, under Additional members, click Invite Member.
-
In the Invite Member panel that opens:
-
Under Provider, select the identity provider in which the member to add is defined. When logging in to the Coveo Administration Console, the member must enter the credentials they use to log in to this third-party application.
Select Single sign-on if you implemented single sign-on in your organization.
Select Any listed if the member’s email address is linked to more than one of the listed applications and you want to let them choose when they log in to Coveo for the first time.
-
Under Email/Username, enter the email address of the member. If you selected a Single sign-on in step 3, this is the
NameIDvalue that Coveo should expect from the SSO provider. -
Check the Send an email notification box if you want the member to receive an invitation to log in to Coveo. When this option is disabled, the user is only notified of their invitation when connecting to Coveo.
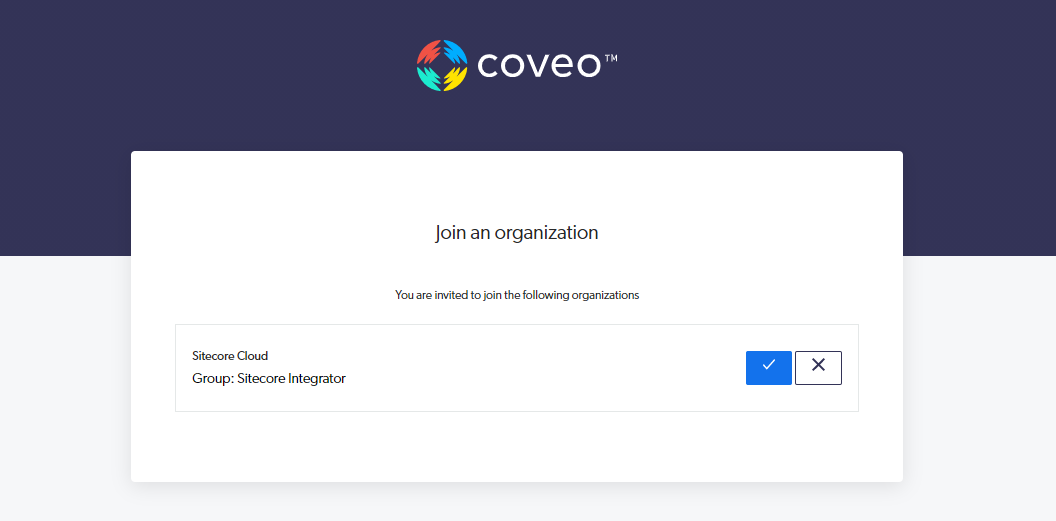
-
-
Click Invite. Your invitation expires after 31 days. Tell the new member which identity provider they should select when logging in to Coveo. The user will appear on the Members (platform-ca | platform-eu | platform-au) page once they accept the invitation.
Delete members from a group
-
On the Members tab, click the member you want to remove from the group, and then click Delete in the Action bar.
-
Click Delete to confirm.
"Privileges" tab
The Privileges tab lists the privileges granted to the members of the selected group. You can edit this list to grant or revoke privileges.
See Navigating the "Privileges" tab and Grant privileges for more information on how this tab is organized. Also see Privilege reference for an exhaustive list of the abilities associated with each domain and access level.
Coveo recommends reviewing the rest of the Manage privileges documentation before granting or revoking any privilege.
|
|
Leading practices
|
"Access" tab
On the Access tab, specify whether each group (and API key, if applicable) in your Coveo organization can view or edit the current group.
For example, when creating a new group, you could decide that members of Group A can edit its configuration, while Group B can only view it.
For more information, see Custom access level.
Completion
-
Once you’re done, click Add group or Save.
-
If you just created a new group, add at least one member:
-
Back on the Groups (platform-ca | platform-eu | platform-au) page, click the group, and then click Edit in the Action bar.
-
On the Edit a group subpage, in the "Members" tab, add one or more members.
-
Duplicate a group
On the Groups (platform-ca | platform-eu | platform-au) page, click the group that you want to duplicate, and then click Duplicate in the Action bar.
The duplicate of the original group has a name in the following format: [OriginalGroupName]_copy.
You can edit this group to change its name or any other aspect of its configuration.
|
|
Note
You can only duplicate groups that are granted fewer privileges than yours. |
Your group has been granted the four following privileges:
| Service | Domain | Access level |
|---|---|---|
Analytics |
View all reports |
Allowed |
Organization |
Activities |
View |
Organization |
Groups |
Edit |
Organization |
Organization |
View |
You can therefore duplicate groups that have three or fewer privileges.
Delete a group
|
|
Note
You can’t delete the Administrators group. |
-
On the Groups (platform-ca | platform-eu | platform-au) page, click the group you want to remove from your organization, and then click Delete in the Action bar.
-
Click Delete to confirm.
Review the activity regarding groups
As part of your duties, you may need to review activities related to groups for investigation or troubleshooting purposes.
To do so, in the upper-right corner of the Groups (platform-ca | platform-eu | platform-au) page, click .
See Review resource activity for details on activities and alternative ways to access this information.
Required privileges
By default, members of the Administrators built-in group can create and edit groups. See Manage privileges for more information on API key or member group privileges.
See Privilege reference for more information on typical privilege grantees and grantee abilities for each domain.
The following table indicates the privileges required to view or edit elements of the Groups (platform-ca | platform-eu | platform-au) page and associated subpages.
| Action | Service | Domain | Required access level |
|---|---|---|---|
View groups |
Organization |
Activities |
View |
Groups |
|||
Organization |
|||
Edit groups |
Organization |
Activities |
View |
Organization |
|||
Groups |
Edit |
|
|
A member with the View access level on the Activities domain can access the Activity Browser. This member can therefore see all activities taking place in the organization, including those from Coveo Administration Console pages that they can’t access. |