Grant privileges
Grant privileges
This is for:
System AdministratorThe operation of granting privileges isn’t to be taken lightly, as insufficient privileges can hinder task accomplishment, while inadequate or unnecessary privileges could lead to accidents or misuse.
When allowed to delegate powers, you should have a good understanding of how the Coveo privilege system works and be aware of the implications of each choice you make. Thoroughly read the privilege documentation before granting privileges or editing a privilege set, and enforcing the principle of least privilege, that is, granting just enough privileges for the grantee to perform their task.
Moreover, to help you use the privilege system safely and efficiently, this page guides through the process of granting privileges to API keys or to other users of the Coveo Administration Console. Coveo encourages you to use this page as a reference until you’re fully comfortable managing privileges.
|
|
Note
To grant privileges to an existing group, you must have the privilege to edit this group. To create a new group and grant it privileges in the process, you need the privilege to create groups. Moreover, for each privilege you want to grant, you also need to have the target access level yourself. See Confirm your options for more information. |
Select a grantee
Depending on your intention, the privilege grantee is either an API key or a group of users. For example, to grant an application the privilege to query your Coveo index, you should create an API key with the appropriate privileges for the application to use when communicating with Coveo. Conversely, to grant Coveo users certain privileges, you should opt for a group of one or more users.
If you choose to grant privileges to a group of users, you have several options:
-
You can create a new group from scratch and grant it the desired privileges. This is the safest option, albeit the most time-consuming.
-
You can duplicate the group with the privilege set closest to the desired set and edit the privilege set of the copy. You can then add the users to this new group.
-
You can pick the unused built-in group with the privilege set closest to the desired set, and then edit these privileges to tailor them as needed.
|
|
Note
For users in more than one group, the highest access level granted for each domain applies in case of conflict. |
Determine the privileges to grant
Once you’ve selected a grantee, you must determine which privileges you want to grant them. To do so, make a list of the operations the grantee should be allowed to perform, the information they should be able to access, etc. Then, associate the domains and access levels corresponding to these actions.
You need an API key to send analytics events to Coveo Analytics and to view usage analytics reports. This API key therefore needs two privileges in the Analytics service:
-
Push on the Analytics data domain.
-
View on the Reports domain.
The Privileges reference page contains a list of all available domains and access levels, and the associated capabilities.
You can also find a list of the privileges required for certain actions in the Coveo Platform documentation. This information is especially important since a View or Edit access level on a domain alone isn’t necessarily sufficient to view or edit the content of the corresponding page, despite most domain names being similar to the names of the Coveo Administration Console pages. Other privileges may be required to view or edit the content of an Administration Console page.
For each Administration Console page, you can find its corresponding list of required privileges in the Required Privileges section of the page’s documentation. To find specific documentation, you can do one of the following:
-
Search for the title of the page in Coveo’s documentation to find the page’s corresponding documentation.
-
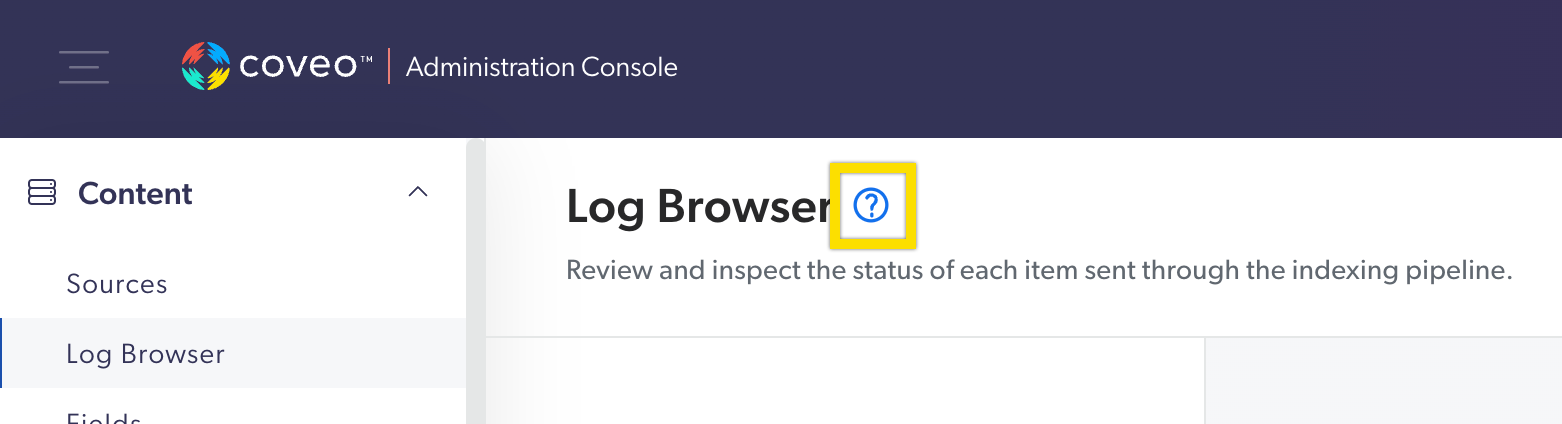
In the Coveo Administration Console (platform-ca | platform-eu | platform-au), click the question mark next to the page title to directly open the corresponding documentation.
Confirm your options
For each domain, the access level you can grant to a group or API key depend on the access level you have yourself, as well as the current access level, if you’re editing an existing group. In short, the list of access levels from which you can choose generally consists of the last saved access level, the access level you have, and the access levels of lesser importance than those.
Before you can grant privileges, you should therefore ensure that your own privilege set allows you to give the desired privileges.
If you’re a member of the Administrators built-in group, you can edit everything in the Administration Console and therefore grant all privileges. If you’re not, you ensure that your own privilege set doesn’t prevent you from granting the desired privileges. Should they be insufficient, you ask a Coveo user with a sufficient privilege set (for example, an administrator) to either grant you the required privileges, or to give the target grantee the desired privileges themselves.
You’re allowed to edit the Content Viewers group. This group has the View access level for the Fields domain, while you have Edit. When changing the group’s access level for this domain, you can choose from your access level, those of lesser importance, and the original group’s access level, that is, Edit, View, or no access at all.
Remarks
After switching from a higher access level to a lower level, you may not be able to grant the higher level again if you’re not yourself granted this higher access level.
You’re allowed to edit groups and to view fields, and you want to revoke the privilege of the Content Manager group to edit fields.
Since your access level options for the Fields domain consist in the last saved access level (Edit), the access level you have (View), and the access levels of lesser importance than those (no access), you can choose from Edit, View, and no access at all.
You switch the Fields domain access level from Edit to View and save, so the last saved access level is now View.
Then, the next time you edit the privileges of the Content Manager group, your access level options for Fields are only View and no access at all, since you don’t have the Edit access level on Fields yourself.
Similarly, if only one of your groups grants you a higher access level on a certain domain and you edit this group’s privilege set to select a lower access level for this domain, you will permanently lose the higher access level after saving.
You’re a member of several groups, but only the Group Managers group grants you the privilege to edit groups.
You no longer want the Group Managers group to be able to edit groups, so you switch its Groups access level to View.
Once you save, you lose your privilege to edit groups and can only view them, as Group Managers was the only group that granted you the Edit access level for the Groups domain.
Grant privileges
Once you have a list of the privileges you want to grant and have ensured that your own privilege set allows you to grant them, you can proceed in the Privileges tab.
-
In the Coveo Administration Console, depending on your grantee, access the Groups (platform-ca | platform-eu | platform-au) or API Keys (platform-ca | platform-eu | platform-au) page. See Select a grantee for details.
-
Create a group or API key, or choose one to edit. To edit an existing group or API key, select the desired item in the list and click Edit in the Action bar.
-
On the Configuration tab, enter or review the basic resource information.
-
In the Privileges tab:
-
Use the menu on the left to navigate the services. For each domain in each service, select the desired access level.
Alternatively, you can use the Template menu to quickly and broadly grant privileges, and then edit only the desired privileges.
-
If editing an existing group or resource, you can discard any change with which you’re not satisfied.
-
If your grantee is a group, ensure to include the minimum privilege so that the grantee can access the Coveo Administration Console.
-
Make sure to review any warning that appears.
-
-
On the Access tab, review which groups or API keys can edit the resource.
-
At the bottom of the panel, click Save.
-
If the grantee is a group, invite members in the group or review the list of members.
Minimum privilege
The View access level on the Organization domain in the Organization service is required for a group of users to access your organization in the Coveo Administration Console. It’s the minimum privilege required—without it, they can’t access any information relatively to your organization, even if they have other privileges.
API keys, however, don’t require this privilege to access your organization content.